Early Bird Gets the Fraudster: How to Stop Credit Application Fraud
A preemptive and UX-friendly approach to credit funnel optimization
A preemptive and UX-friendly approach to credit funnel optimization
It’s one thing to Know Your Customer; it’s another to Know Your Con-Artist. KYC checks, ostensibly, prevent banks from doing business with bad actors, but doing so requires neutralizing fraudsters at the point of entry, before they’re able to apply for a loan.
In other words: early bird gets the fraudster.
A preemptive strategy is the only realistic way to effectively prevent credit application fraud—when a fraudster submits personally identifiable information (PII) to apply for credit (credit card, loan, etc.). This approach saves banks from running costly, unnecessary credit checks on fraudsters, and ensures genuine customers are identified up front and not wrongfully declined. It also curbs the risk of fraudsters slipping through the credit application process scot-free. In a 2018 study, one major North American bank issued 1,400 credit cards per month to fraudsters—a loss of ~$500,000 per month.
But is spotting fraud pre-credit application, before the verification stage, even feasible?
A never-ending money hole
Before we discuss the practicality of shutting down fraudsters pre-credit application, let’s look at the two glaring downsides of not adopting this approach. Problem number one: credit application fraud can be a significant money pit (and time suck) for banks.
Factoring in the cost of running a credit application through third party sources—namely, multiple credit bureaus—can cost between $3-5 per application. The fraudster may then be asked to verify their document, a fabricated driver’s license matching their details, which costs the bank another $3-4 per applicant. Manual review alone can cost another $50-75. And, since synthetic identity fraud is now the largest form of identity fraud in the country, there’s a good chance banks could be chasing a made-up, nonexistent entity.
Synthetic identity fraudsters, whose fake identities are stitched together using bits and pieces from real identities, exploit the very processes that banks and fraud solutions rely on. For example, most banks look for static PII data such as a social security number or date of birth when analyzing credit applications, which is easily obtainable from the dark web. Additionally, synthetic fraudsters will often apply for credit with two lenders to compensate for the identity’s lack of credit history. Ironically, the first lender’s rejection of credit will usually initiate a credit file that enables the second credit application to go through. Low credit limits? Synthetics can work around that, too. A few small transactions here and there, paid off at the end of the month, and they can steadily increase their spending limit until it’s worthwhile to cash out.
A churn for the worst
Not detecting fraud until after the credit application process lets more fraudsters in. It also keeps more good users out.
For instance, geography is a common false positive trigger if a user has recently moved. After this user fills in their basic info, including their address, and creates an account, you can almost guarantee a red flag from the credit bureau. The new address doesn’t match what’s on file. Next step? Document verification. And if users are still around at that point, banks should count their lucky stars.
Legitimate users with thin files are the most likely to get declined. “Thin file” refers to applicants whose credit history is so sparse that standard fraud prevention tools lack the data to calculate risk. A thin file applicant might be a student applying for their first credit card. Other examples include immigrants without credit history in the US; consumers who haven’t used credit in a long time; and people who predominantly use cash over credit.
According to an Experian report, about 62 million Americans have a thin file.
Unlike synthetic fraudsters, who are cunning enough to establish a semblance of credit history by applying to multiple lenders, genuine identities with thin files are often automatically declined. Many of these rejected users will apply to another bank, resulting in churn and lost revenue. Even worse, a substantial amount of unfair declines could harm a bank’s reputation over the long term.
It starts at the top
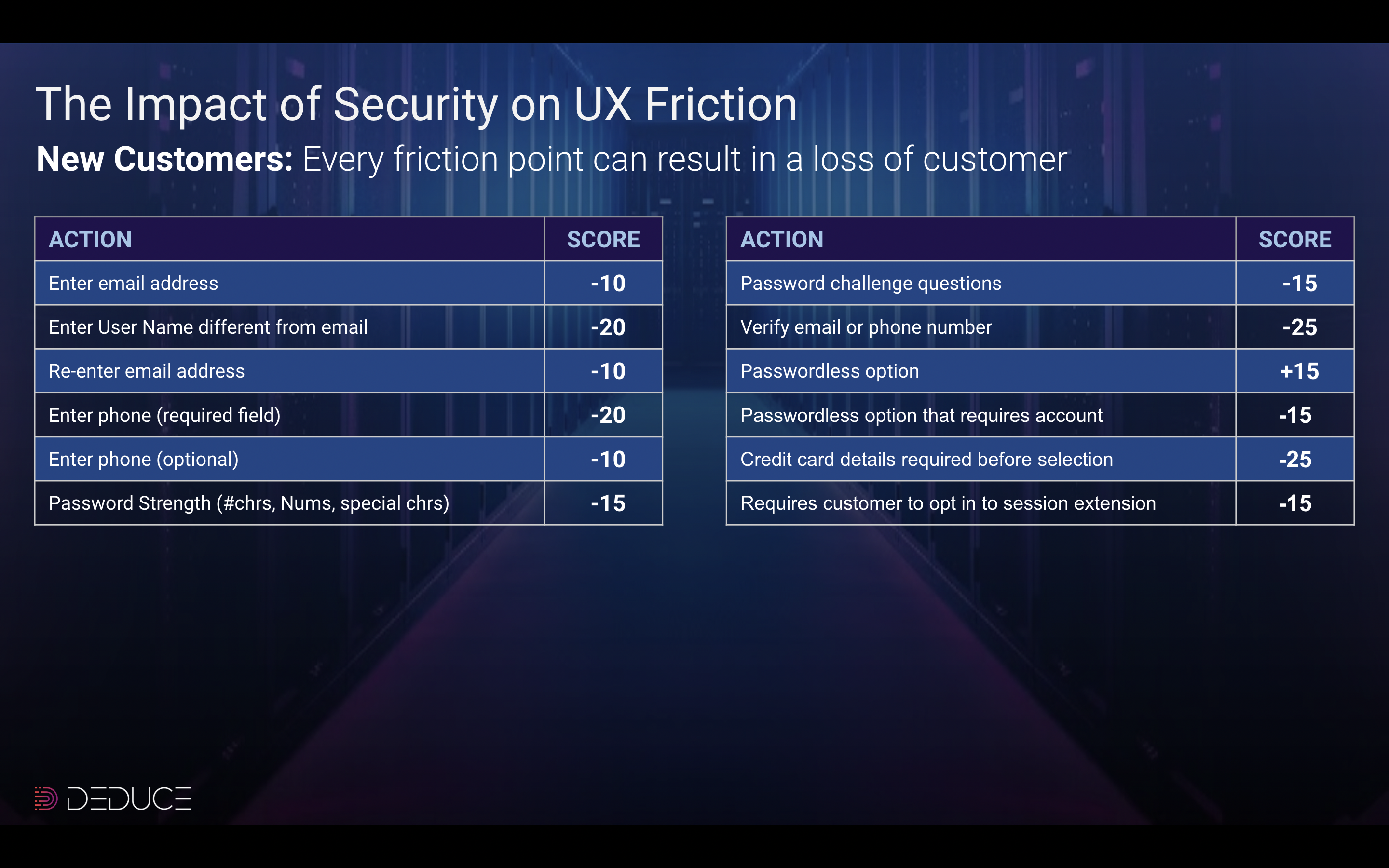
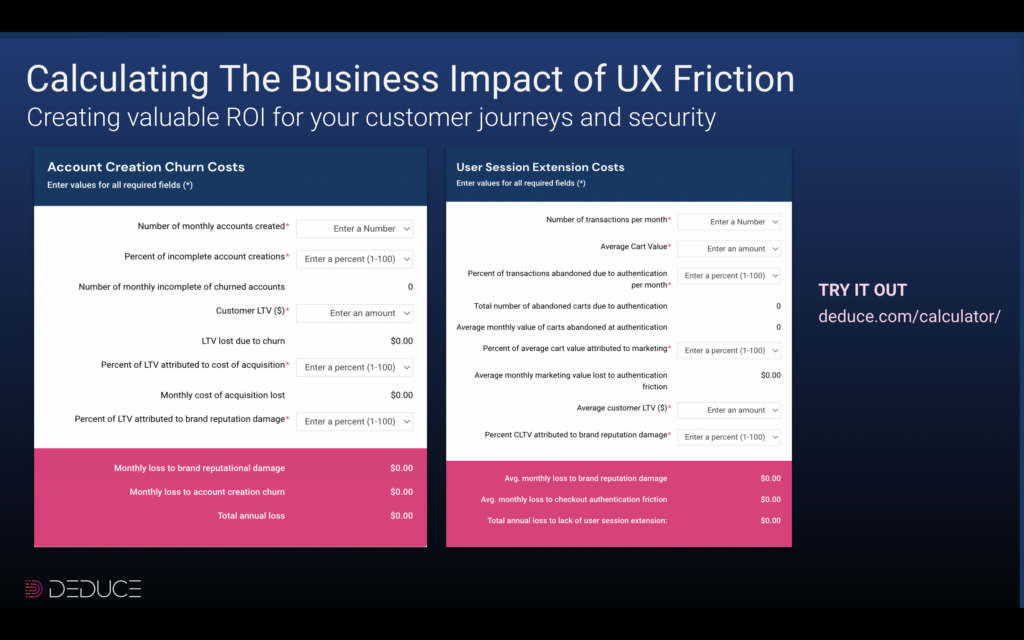
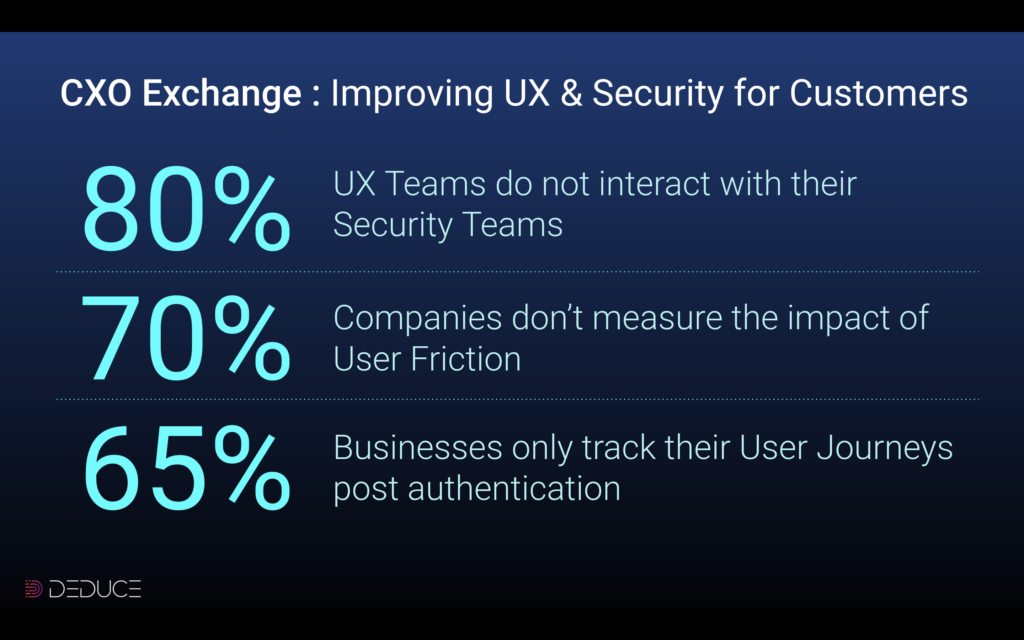
We’ve established that preventing credit application fraud and false positive declines isn’t tenable unless banks act before applicants apply for credit. But rearranging the UX and security for the credit application process isn’t entirely an in-house operation. It requires assistance from a powerful and highly intelligent first line of defense, with a data stack that rivals the FAANG gang.
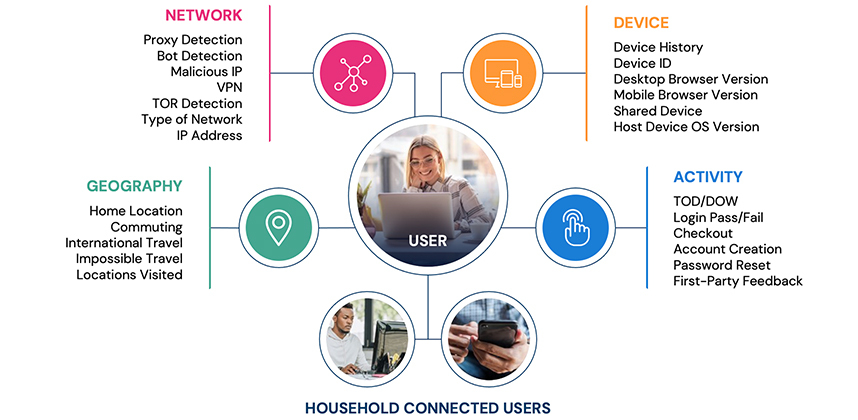
Deduce’s real-time identity network fits the description: 660 million US privacy-compliant identity profiles and 1.5 billion daily user events across 150,000+ websites and apps. With this magnitude of data powering their credit app fraud prevention efforts, banks can identify fraudsters and legitimate users pre-credit application, effectively bridging security and UX.
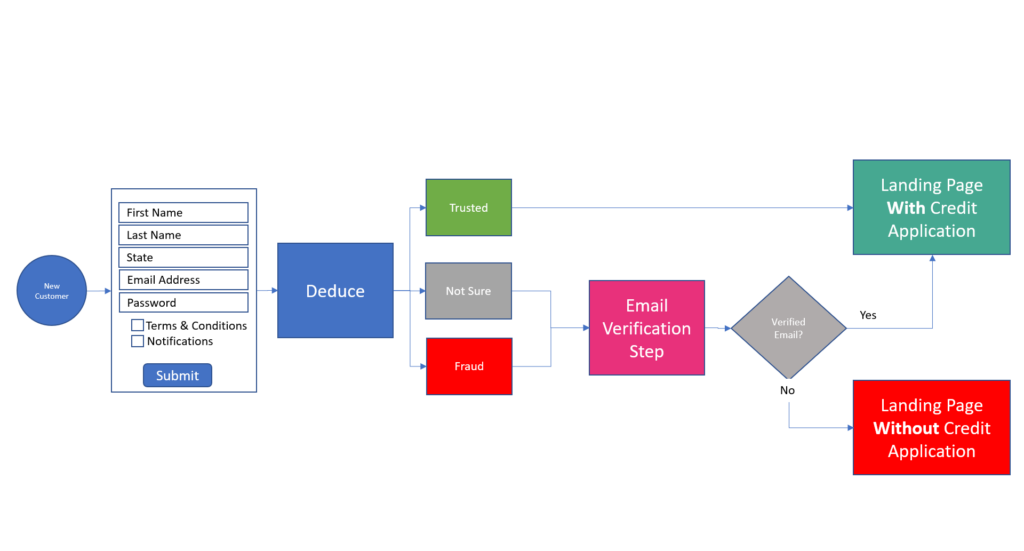
As illustrated in the graphic above, if the Deduce Identity Network deems the user a fraudster, they’re sent to a landing page devoid of a loan or credit application option; if the user is legit, they’re presented with a list of loan or credit options that fit their needs. This is credit funnel optimization done right.
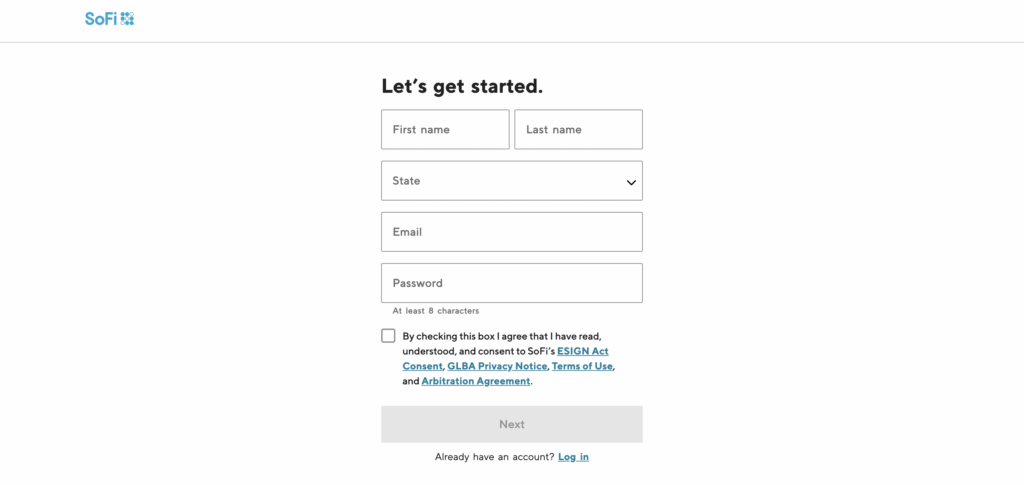
It’s no wonder that some leading financial institutions, such as SoFi, have adopted this preemptive, highly optimized approach to their credit application journeys. Aside from thwarting fraudsters and false positives, and improving conversion rates, checking for fraud upfront assists marketing efforts. If a new user is determined to be genuine but rejected because of their credit score, the initial collection of their contact info allows banks to keep in touch. That way, users aren’t lost in the sauce and can reapply in the future once their credit score reaches the required threshold.
There’s no better way to shut down credit app fraudsters who’ve grown accustomed to banks’ antifraud processes. Preventing false positives and salvaging quality customers is vital in its own right, and may prove even more so in the grand scheme of things. By placing Deduce at the forefront of your credit app fraud strategy, the marriage of security and UX is indeed possible, and bottom lines will be all the better for it.
Ready to shut the door on credit application fraud? Contact us today and get up and running in a few hours.