Robinhood Breach Underscores Danger of Account Takeover
ATO hits companies hard. It only gets worse downstream.

ATO hits companies hard. It only gets worse downstream.
It’s been an eventful year for embattled trading platform Robinhood. Following its infamous biff with “meme stock” investors in January, leading to lawsuits and congressional hearings (and an upcoming Netflix movie), the company went public in July but failed to inspire much excitement around the IPO.
Before Robinhood could lick its wounds and hope for a better 2022, they suffered another setback in early November: a data breach that impacted more than 7 million customers. The breach snatched names, emails, dates of birth, and — to the delight of robocallers — thousands of phone numbers.
You might think, “No credit card or social security numbers leaked? What’s the big deal?” but bad actors don’t need much to harm consumers.
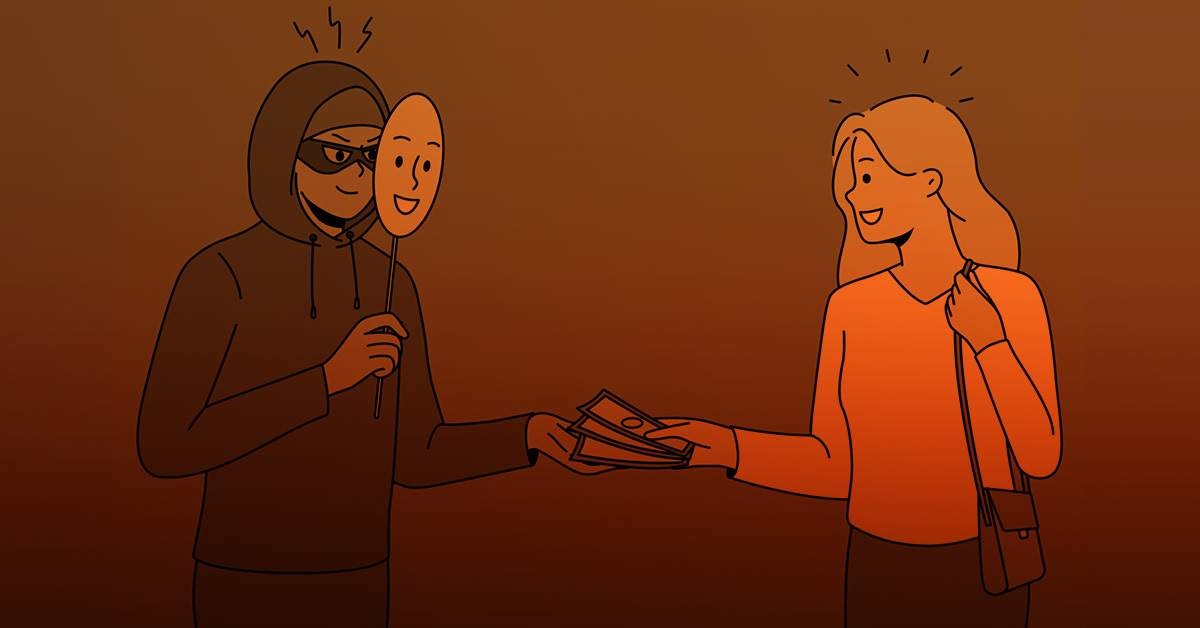
Here is how stolen account information, even seemingly innocuous details like names and dates of birth, can lead to account takeover fraud (ATO) and cause further damage downstream.
A dark reality
Stolen account information is trafficked in the nefarious underworld known as The Dark Web. In what’s essentially a farmer’s market for fraudsters, tens of thousands of account credentials are up for grabs at any given time, some going for as much as $15,000.
Personal information acquired from data breaches is another valuable commodity among Dark Web shoppers. These days, name, date of birth — a zip code in some cases — can be used to verify a customer’s identity. Hackers also leverage data mined from The Dark Web to plan and execute phishing attacks or aid other ATO schemes, such as credential stuffing.
The biggest danger of ATO, however — particularly at the scale of the Robinhood breach — is its ability to metastasize, potentially costing millions in chargebacks, not to mention time spent on remediation and navigating a PR firestorm.
A storm with no calm
The worst part of an ATO breach is the aftermath. Per Javelin Research, customers pay an average of $290 for every successful ATO attack and spend 15–16 hours disentangling the wreckage. Not a fun time for customers — or customer support teams.
Many of the users affected by ATO are likely to flee and seek out other platforms. 85 percent of respondents from a recent CMO Council report indicated they dislike companies with identity verification issues; ostensibly, a breach resulting in ATO fraud bumps this number into the 90th percentile. And what will they do after jumping ship? Air their grievances, which — in aggregate — deals a hefty blow to a company’s brand image. It’s the polar opposite of a Trusted User Experience that encourages loyalty, and, depending on the degree of damage, can be difficult to come back from.
To protect against ATO and its residual impacts, companies need to adopt the data-driven, pre- and post-authentication security approach of a Deduce. Our real-time Identity Network comprises more than 450 million anonymized user profiles collected from 150,000 websites and apps, offering preemptive protection that tips off companies long before ATO can manifest.
Want to give Deduce a go? Try a free trial here.