Device Fingerprinting: ATO Liability, Bearer of False Positives
Device fingerprinting is moot without real-time identity intelligence

Device fingerprinting is moot without real-time identity intelligence
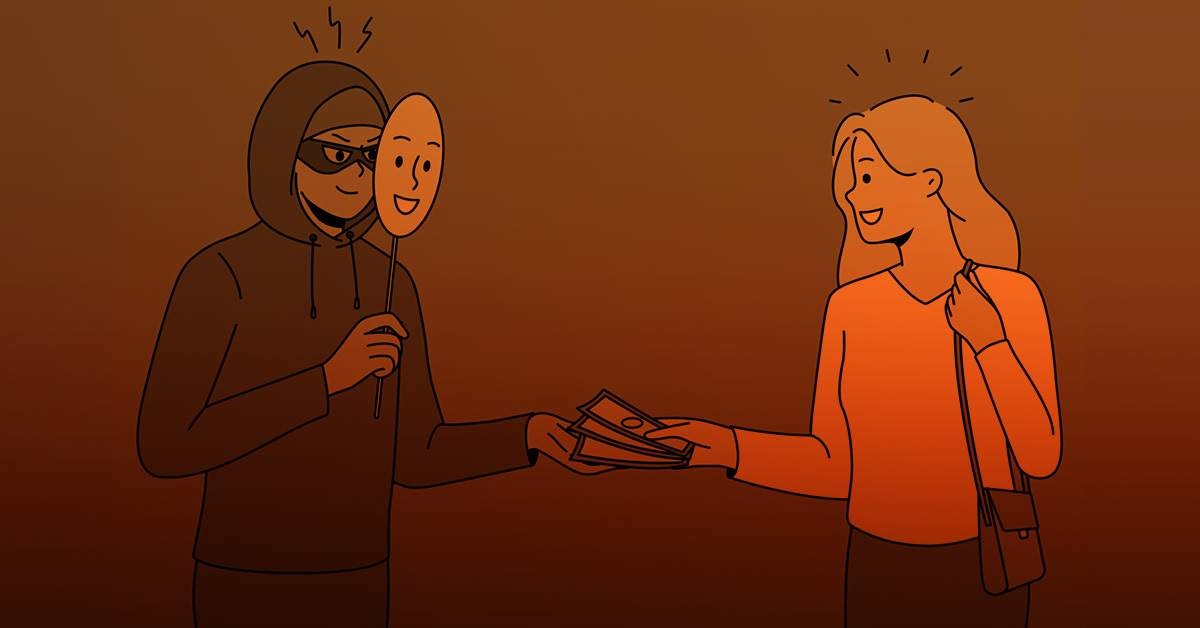
Device fingerprinting, a way of positively identifying a device by recognizing its unique software and hardware characteristics, used to be enough to prevent identity fraud. Not anymore.
The list of factors device fingerprinting tracks — IP address, installed fonts, flash data, VPN/browser details, battery info, etc. — may seem sufficient to prevent fraud and false positives. But today’s fraudster can easily spoof these parameters, and the multitude of devices in our lives, each carrying a unique fingerprint, increases the likelihood of a legitimate user getting flagged incorrectly.
Like an old mall cop who can’t chase down shoplifters without his trusty Segway, device fingerprinting requires similar augmentation in the form of real-time insights.
Here is why augmenting device fingerprints is imperative to correctly identifying users and bad actors, and how adding real-time trust signals to the mix forms the perfect one-two punch.
You get a fingerprint, you get a fingerprint, you get a fingerprint
Akif Khan, a Senior Director at Gartner Research, points to three primary reasons as to why device fingerprinting — in and of itself — isn’t viable as a long-term, comprehensive fraud solution:
- Device and fingerprint overload. Many users spend time on multiple devices each day — phone, laptop, tablet — with a unique fingerprint assigned to each. Without real-time data, a device fingerprinting could easily flag a good customer if they transacted across more than one device.
- Reliable fingerprints are hard to come by. User privacy and device fingerprinting don’t exactly go hand in hand. Anti-cookie sentiment, private browsing, and the plethora of browsers at users’ disposal contributes to inconsistent fingerprinting. Khan asked some fraud prevention vendors if their solutions would detect the same fingerprint across different browsers on the same device — only one said yes.
- Beware of malware. Fraudsters are finding more ways to execute malware-based attacks and remotely access a user’s device. Once a device and its fingerprint is hijacked, a bad actor can do as they please.
Khan, while transparent about its shortcomings, agrees that device fingerprinting plays an important role in mitigating fraud. However, without an intelligence layer stacked on top, many fraudsters will find a way to execute ATO (account takeover) attacks and honest customers will be unnecessarily flagged. These outcomes can add friction to the customer journey, cause churn, and harm company reputations.
There’s no time like real-time
Real-time data is the missing link in the device fingerprinting dilemma.
A single user logging into multiple devices can generate red herring security alerts, but a fingerprinting solution coupled with real-time analytics intelligently verifies a user’s identity with no added friction. Similarly, real-time identity intelligence checks for additional data points that counteract fraud tactics like device spoofing, in which bad actors use web browsers that mask operating system data and sometimes create fake virtual environments to throw device fingerprinting off the scent.
The real-time data needed to augment device fingerprinting includes risk signals like impossible travel, device downgrade, network risk, and previously unseen email, among dozens of others, as well as trust signals such as familiar network, familiar device, and familiar city. However, neutralizing ATO and false positives consistently requires identity intelligence, real-time data on a profile’s activity across the consumer web. This type of external visibility — in concert with device fingerprinting — yields a much smarter authentication risk control plane thanks to a scoring system that is able to link millions of user touch points together.
Here are two scenarios that benefit from the dynamic duo of device fingerprinting and real-time identity intelligence:
- A user has three browser fingerprints on a given website from the same device: one fingerprint from an earlier version of Chrome, one from the latest version, and another from Chrome with new plugins installed. Linking this data with activity data across thousands of websites, the risk engine intelligently links and resolves, reducing unnecessary false positives.
- A given IP that has been shown (and confirmed by third-party sources) to be a benign residential IP node suddenly sees a spike in authentication failure paired with many new attempted usernames. It’s inferred that there is malicious activity (typically indicative of a compromised node).
At Deduce, these intricate login and authentication events pop up thousands, if not millions, of times per day. By correlating event-level telemetry data, augmentative data sources, and first- party feedback data, Deduce adds an intelligence layer to device fingerprinting that keeps the good people in and the bad people out. Powering these insights is the Deduce Identity Network, a consortium of 150,000+ websites and apps that sources the maximum amount of real-time activity data for a given user. To date, this has netted over 450 million unique identity profiles that generate more than 1.4 billion daily observations.
Want to mitigate ATO and false positives? Click here to see how Deduce can augment device fingerprinting and give your customers peace of mind.