Coopetition is the Panacea for Data Poverty in Cybersecurity
Competing security companies can unite to fight fraudsters and still remain competitive

Competing security companies can unite to fight fraudsters and still remain competitive
More data = more accuracy. This is generally a well-understood truth in any data-applicable field, from economics to medicine to machine learning. Fortunately, we live in an era awash in data; the abundance of data underpins the success of businesses across various industries — except in cybersecurity, where there is actually a dearth of actionable data.
Data poverty in cybersecurity is a profound problem for businesses and consumers. It means cybersecurity systems lack access to the grade-A data needed to effectively prevent the next enormous data breach. It means security systems lack the data insights to effectively identify insidious hacker patterns.
What’s the solution to the data poverty in cybersecurity? Data coopetition.
Data Coopetition: a Proven Model in Many Industries
Data coopetition is data sharing between businesses, even rival ones, to achieve a common goal. It’s an existing practice in several industries, for example:
- Casinos exchange intelligence on card counters.
- Rival software companies exchange data to make more money and improve the customer experience.
- Adtech businesses collaborate to deliver more effective brand campaigns.
- Healthcare providers exchange patient data, enabling doctors to accurately diagnose diseases and save lives.
- The FS-ISAC (Financial Services — Information Sharing and Analysis Center) is a consortium of 15,000 businesses in the financial sector collaborating to safeguard their respective institutions and customers from cybercrime.
Yet data coopetition is woefully absent in cybersecurity, the very mitigators of cybercrime. Why? The simple answer is competitive advantage: cybersecurity companies are reluctant to share data for fear of giving their competitors an advantage. However, as exemplified by other industries, data sharing isn’t a zero-sum game; actionable data can be exchanged in a secure and privacy-compliant way with the right solution.
Data Democratization on a Privacy-Compliant Basis
No cybersecurity vendor is data-rich. Sharing timely and functional behavioral data on cyberthreats benefits all vendors working to neutralize bad actors. For example, companies can exchange data on attack reports, which provide the code used to defend against an attack. Another example is sharing datasets of typical user behavior, such as how often they mistype their passwords, in order to identify anomalies in user patterns that indicate unauthorized access.
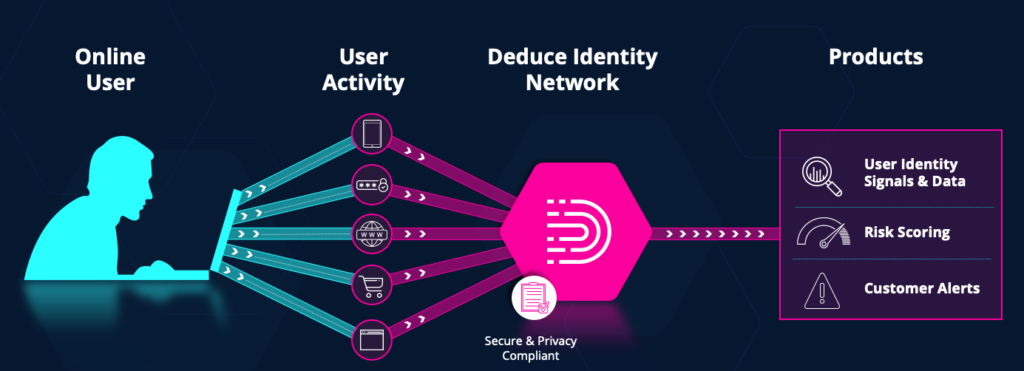
How can cybersecurity companies share data in a secure way that doesn’t compromise competitive advantage? Deduce was founded to address this data democratization opportunity. We created a data collective through which companies can share information about users’ security-related behavior and logins. In exchange for sharing data with the platform, companies get access to Deduce’s repository of identity data from over 150,000 websites, which is used to better detect suspicious activity and alert their users.
It’s Time to Shift the Cybersecurity Mindset
To protect businesses and their customers from fast-evolving fraudsters, the industry must shift its mindset — we have no other choice. Companies gain no competitive advantage by hoarding cybersecurity data. Even worse, it leaves everyone vulnerable. We need to think more along the lines of other industries that already realize the value of shared data. By adopting a collective intelligence model, cybersecurity companies have a fighting chance against hackers.
See Deduce in action! Click here to request a demo.